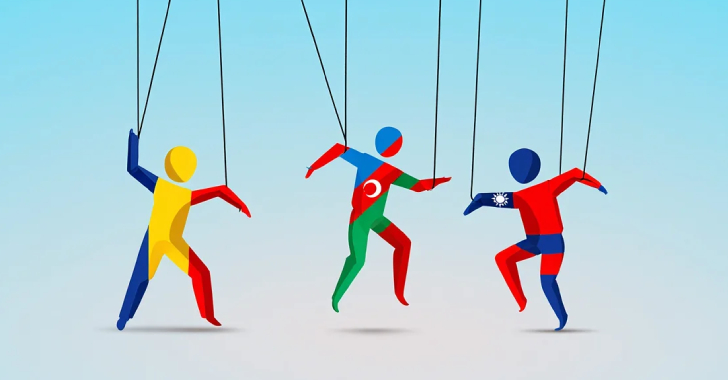
Meta on Thursday revealed that it disrupted three covert influence operations originating from Iran, China, and Romania during the first quarter of 2025.
“We detected and removed these campaigns before they were able to build authentic audiences on our apps,” the social media giant said in its quarterly Adversarial Threat Report.
This included a network of 658 accounts on Facebook, 14 Pages, and
Source: Read More