PumaBot: New Stealthy Linux Botnet Evades Detection, Targets IoT Devices
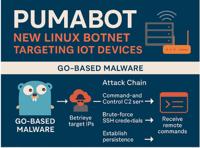
Cybersecurity researchers at Darktrace have exposed a stealthy and persistent Linux-based botnet dubbed PumaBot, which leverages Go binaries, SSH brute-force attacks, and custom backdoors to target In …
Read more
Published Date:
Jun 01, 2025 (5 hours, 47 minutes ago)
Vulnerabilities has been mentioned in this article.
Source: Read More

