Apple has fixed a vulnerability that was used in zero-click attacks that installed Paragon Graphite spyware on the iPhones of two European journalists.
Apple patched the vulnerability – CVE-2025-43200 – in iOS 18.3.1 back in February but didn’t add it to the advisory until this week.
In the Messages vulnerability, “A logic issue existed when processing a maliciously crafted photo or video shared via an iCloud Link,” the updated Apple advisory says. “Apple is aware of a report that this issue may have been exploited in an extremely sophisticated attack against specific targeted individuals.”
While Apple didn’t provide details of the attack, the updated advisory coincided with the publication of a Citizen Lab report that CVE-2025-43200 was used in zero-click attacks to install Paragon spyware on the iPhones of two European journalists.
Paragon Spyware Attacks Detailed
The Citizen Lab report said that on April 29, 2025, “a select group of iOS users were notified by Apple that they were targeted with advanced spyware.”
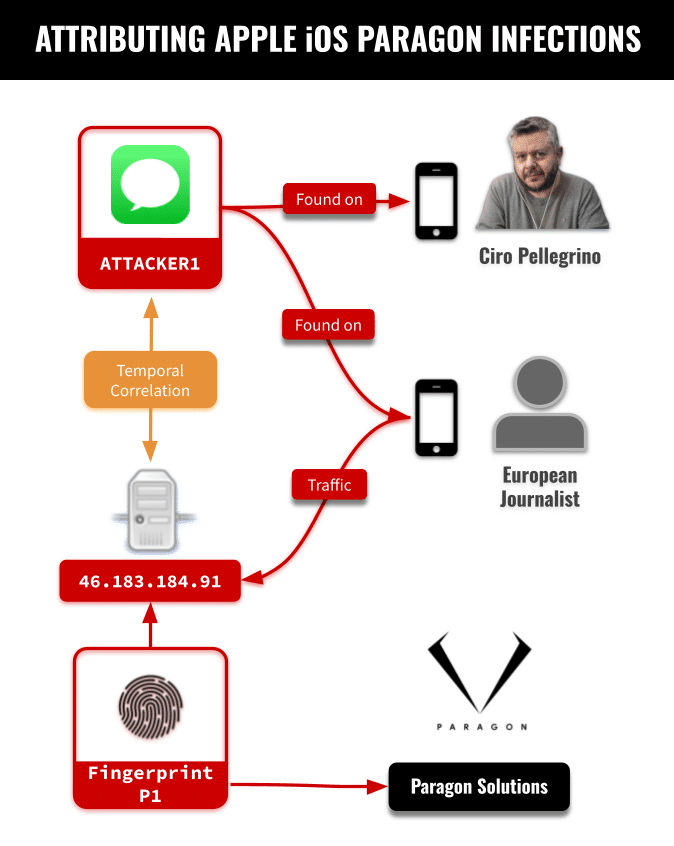
While the size of that group is unknown, two journalists in the group – an anonymous European journalist and Italian journalist Ciro Pellegrino – provided their devices to Citizen Lab for technical analysis. That analysis linked the targeting of the two journalists “to the same Paragon operator,” the Citizen Lab report said.
The Paragon operator and the reasons the journalists were targeted remain unknown.
Citizen Lab said its forensic analysis concluded that the anonymous journalist’s device was compromised in January and early February 2025 while running iOS 18.2.1. Logs on the device “indicated that it made a series of requests to a server that, during the same time period, matched our published Fingerprint P1. We linked this fingerprint to Paragon’s Graphite spyware with high confidence.”
An iMessage account was identified in the device logs around the same time that the phone was communicating with Paragon server 46.183.184[.]91. “Based on our forensic analysis, we conclude that this account was used to deploy Paragon’s Graphite spyware using a sophisticated iMessage zero-click attack,” Citizen Lab said. “We believe that this infection would not have been visible to the target.”
The same iMessage account appeared in the device logs of Pellegrino’s iPhone, “which we associate with a Graphite zero-click infection attempt.”
As each customer of a mercenary spyware company typically has their own dedicated infrastructure, the account “would be used exclusively by a single Graphite customer / operator, and we conclude that this customer targeted both individuals.”
Links to Other Paragon Spyware Cases
Pellegrino was the second journalist at Fanpage.it known to be targeted with Paragon spyware, suggesting that the news organization itself may have been a target.
In the first Fanpage case, editor Francesco Cancellato was notified in January 2025 by WhatsApp that he was targeted with Paragon spyware.
“At the time of publishing, three European journalists have been confirmed as targets of Paragon’s graphite mercenary spyware,” Citizen Lab said. “… Yet to date, there has been no explanation as to who is responsible for spying on these journalists.
“Furthermore, the confirmation of a second case linked to a specific Italian news outlet (Fanpage.it) adds urgency to the question of which Paragon customer is responsible for this targeting, and pursuant to what legal authority (if any) this targeting took place.
“The lack of accountability available to these spyware targets highlights the extent to which journalists in Europe continue to be subjected to this highly invasive digital threat, and underlines the dangers of spyware proliferation and abuse.”
Source: Read More