Linux Sudo chroot Vulnerability Enables Hackers to Elevate Privileges to Root
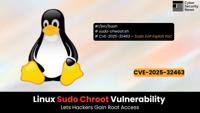
A critical security vulnerability in the widely used Linux Sudo utility has been disclosed, allowing any local unprivileged user to escalate privileges to root access.
Summary1. CVE-2025-32463 affects …
Read more
Published Date:
Jul 01, 2025 (1 hour, 13 minutes ago)
Vulnerabilities has been mentioned in this article.
Source: Read More

